If you are on less than Ghost 6.19.1, it's way past time to upgrade
And you might need to roll your keys, too.

Hey self-hosting folks,
REMINDER: I don’t work for Ghost. The content below is my own opinion, not that of the Ghost Foundation, blah blah blah. Might be wrong, and possibly worth only what you paid for it (nothing).
In case you’ve missed it, Ghost had a baaad security vulnerability back in February, disclosed here:
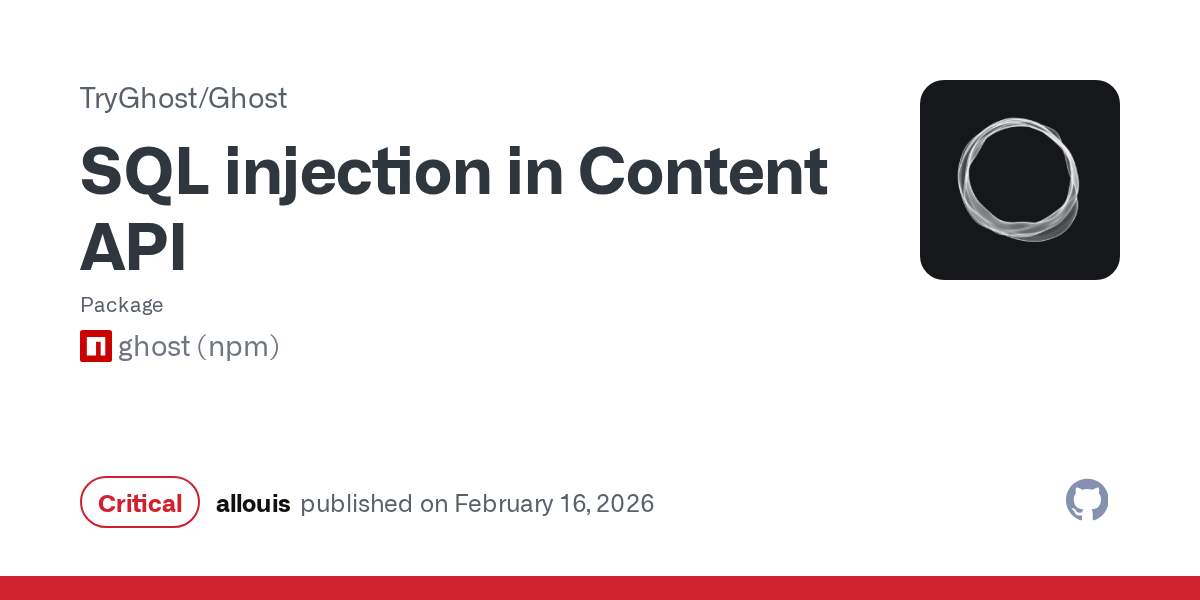
That’s a bad one. Specifically, it allows an attacker to read your whole site, include admin api keys, and once they’ve got the admin api key, there’s a lot that can go wrong.
So, if you’re self hosting, you should IMMEDIATELY upgrade. Do not pass go, do not collect $200, just upgrade. (The vulnerability is there all the way back to 3.x, so older sites are not safe.)
If you updated right when 6.19.1 was released, it might be ok to assume that your site wasn’t compromised before you updated, since the vulnerability probably wasn’t widely known… maybe. If you’re still at < 6.19.1 NOW, you need to seriously consider the possibility that attackers might already have your admin api key, and that upgrading will remove the ability to get a key, but not fix any existing key leakage.
My possibly over-cautious thought is that you absolutely need to upgrade immediately, and then you should probably roll all your keys, including staff tokens. I’m not sure if this is overly alarmist, but better safe than sorry? My thinking here is that
NOTE: If you have services connected through these keys, you WILL break them by doing this. You’ll need to revisit each service and provide the newly regenerated key/token. Yes, that sounds like a pain.
Staff tokens can be regenerated from the individual staff profile (only for the logged in user). Scroll down and click ‘regenerate’. Suspend any admin or enhanced editor users you can’t get to regenerate their own tokens. (Editors with the enhanced editor role can read the members list.)
Your Admin API keys in custom integrations can be regenerated from /ghost > settings > custom - click into each integration and regenerate.
You also need to regenerate your Zapier token - in /ghost > settings > integrations, click ‘configure’ next to zapier and regenerate the token. I’ve seen two reports of sites being compromised via Zapier token, specifically. I’m not sure it’s from this vulnerability instead of a Zapier vulnerability/leak, but I’m suspicious.
That’s all I know. Wanted to get it out there in case it helps someone. Even if key rolling sounds like too much to do today, please please please do yourself a favor and update to >= 6.19.1.
(This is a crosspost with the Ghost forum: https://forum.ghost.org/t/if-you-are-on-ghost-6-19-1-you-really-need-to-update/62706 )
Hey, before you go... If your finances allow you to keep this tea-drinking ghost and the freelancer behind her supplied with our hot beverage of choice, we'd both appreciate it!